Using ssh tunneling to gain access to remote VirtualBox guest attached to NAT
I’m building virtual machines on a weekly basis, sometimes daily. Most often I create various Linux distros as guests on VirtualBox hosts. VirtualBox hosts are either Windows or Linux computers. Majority of guests are built for test purposes only, so they often live in a “cage” behind a VirtualBox NAT. Guests with NIC attached to NAT have access to the LAN and Internet, but the opposite is not possible out of the box. So my typical NIC configuration for VirtualBox guest looks like this:
Fortunately, VirtualBox allows to configure port forwarding for NAT attached NIC’s. For every Linux guest I setup port forwarding for ssh (22), so that I can use MobaXterm (on Windows7/10) to connect to the Linux guest from the host itself. That’s how it looks:
That’s fine, as long as you have access to the host where your VBox guest is running, you can use MobaXterm to connect to the virtualbox guest. Seating at Windows 7 workstation we simply open MobaXterm and type:
Sometimes, I build virtual machines that I want to access from other machines as well and I don’t like to weaken security by attaching guest NIC’s to a Bridged adapter. Again, let’s call wonderful ssh to the rescue.
Situation: VirtualBox host is a Windows 2008 R2 Server (I’ll refer to this host as VBOXHOST). On this host we’re hosting Linux guest (OL7ORA12R2) with the latest Oracle 12.2 installation. Guest is behind a NAT, but with a port forwarding setup for ssh as shown above (picture 3). I would like to have access to this guest from remote workstation running Windows 7. All machines (physical Windows 7 & 2008R2, plus virtual Linux 7) are firewalled with ssh ports (22) left opened. On Windows 2008R2 is already running OpenSSH (Cygwin).
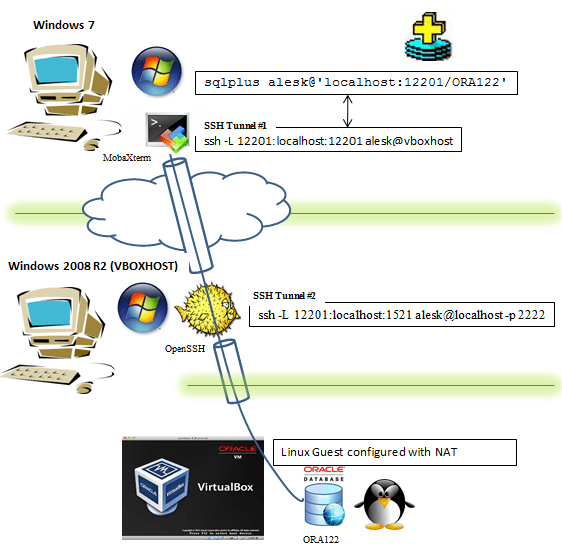
All that we need to do to get sqlplus access to remote Oracle 12.2 running in Linux guest from Windows 7 workstation is this:
On Windows 7 we start MobaXTerm terminal and run (note that by default Mobaxterm uses implicitly -X for ssh): $ ssh -L 12201:localhost:12201 alesk@vboxhost -t ssh -L 12201:localhost:1521 alesk@localhost -p 2222 First, we're asked for password to connect to vbohost (Windows 2008 R2), then we're asked for password to login to virtual machine guest (Linux). Note, that we must left the MobaXterm window open for a duration of SQL*Plus session that follows... Now, we can connect from Windows 7 Workstation to the remote Oracle DB, first open cmd and type: cmd> sqlplus /nolog cmd> connect c##alesk@'localhost:12201/ORA122'
What happens is illustrated on this picture:
- On Windows 7 we launched MobaXterm and run ssh command:
- On Windows 7 we opened sqlplus, connecting to localhost:12201. SSH redirected traffic to VBOXHOST:12201 (hop 1), followed by second redirection (hop 2) to Listener running inside VirtualBox.
$ ssh -L 12201:localhost:12201 alesk@vboxhost -t ssh -L 12201:localhost:1521 alesk@localhost -p 2222 ssh -L 12201:localhost:12201 alesk@vboxhost ........... tunnel #1 forwarding port 12201 (Windows 7) to port VBOXHOST (port 12201), in both cases on localhost. ssh -L 12201:localhost:1521 alesk@localhost -p 2222 .... tunnel #2 forwarding port 12201 (VBOXHOST) to port 1521 inside VirtualBox Guest, using port 2222 redirection done by VirtualBox itself.
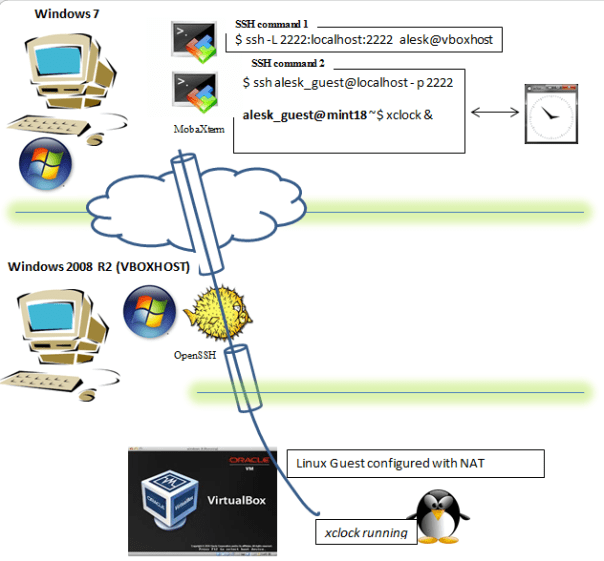
What if we would like to run some GUI application on Linux guest? We can use X session forwarding, allowing us to see the GUI on our Windows 7 workstation. Like this:
We must open two MobaXterm terminals on Windows 7 workstation.
In the first MobaXterm terminal we type:
$ ssh -L 2222:localhost:2222 alesk@vboxhost
In the second MobaXterm terminal we type:
$ ssh alesk_guest@localhost -p 2222 alesk_guest@mint18 ~$ xclock &
….and xclock will popup on Windows 7 workstation but actually running on Linux guest. Note that alesk_guest is a Linux user on LinuxMint 18 guest and that guest is configured in the same way as before, behind a NAT and with ssh port forwarding (2222) at VirtualBox level. This option is handy to lauch Oracle gui configuration tools, like dbca, netca etc.
Posted on 15.03.2017, in Other and tagged Linux, ssh, virtualbox, windows. Bookmark the permalink. Comments Off on Using ssh tunneling to gain access to remote VirtualBox guest attached to NAT.




You must be logged in to post a comment.