How to install and use vpnc to connect to Cisco VPN concentrator
Even though I managed to install Cisco VPN client 4.8 on my Ubuntu (Lucid Lynx) workstation, I was not successful at troubleshooting the connection attempt to our corporate Cisco VPN concentrator. Each attempt of mine to establish VPN connection, ended in greeting with the error message:
Secure VPN Connection terminated locally by the Client Reason: Failed to establish a VPN connection. There are no new notification messages at this time.
I almost gave up my hopes to use Ubuntu for VPN, fortunately, I recently met an Oracle DBA (Igor@3Gen), who told me that he’s is successfully using vpnc to connect to the same Cisco VPN concentrator as I am.
He was kind (thanks Igor!) to share his notes on the subject. This is my resume of steps that I followed to install and configure vpnc (of course, some technical details are obfuscated).
Step 1) Install vpnc and Gnome GUI plugin for network manager
-- -- Install vpnc -- $ sudo apt-get install vpnc $ sudo apt-get install network-manager-vpnc $ sudo apt-get install network-manager-vpnc-gnome
Step 2) Extract group password from Cisco client pcf file
Until now, I was using Cisco VPN client on Windows 7, that was packed and delivered to me by our corporate VPN support team. My Cisco VPN client (v5.0.02.0090) already included the necessary profiles (*.pcf files) with the configuration data. Profile configuration files are usually located in C:\Program Files\Cisco Systems\VPN Client\Profiles.
If you open your pcf file you’ll find (among other data) encrypted group password in the field !enc_GroupPwd. This is a pre-shared secret that we first need to decrypt it and then use it in our vpnc configuration file. Hopefully, this is not hard with the tools that exists on the net.
-- -- 2.1 Prepare working directory -- $ mkdir vpnc $ cd vpnc -- -- 2.2 Install cisco-decrypt from source file -- $ wget http://www.unix-ag.uni-kl.de/~massar/soft/cisco-decrypt.c $ sudo apt-get install libgcrypt11-dev $ export PATH=.:$PATH $ gcc -Wall -o cisco-decrypt cisco-decrypt.c $(libgcrypt-config --libs --cflags) -- -- 2.3 Check that cisco-decryp was built -- alesk@dbaportal:~/vpnc$ ls -l cisco-decrypt -rwxr-xr-x 1 alesk dba 7850 2010-12-04 18:04 cisco-decrypt -- -- 2.4 Download pcf2vpnc -- $ wget http://svn.unix-ag.uni-kl.de/vpnc/trunk/pcf2vpnc $ chmod +x pcf2vpnc -- -- 2.5 Copy your .pcf file from Windows client to our vpnc working directory -- on ubuntu (let's say that our pcf file is called acme-vpn.pcf) -- and run pcf2vpnc against our pcf file. -- $ ./pcf2vpnc acme-vpn.pcf > acme-vpnc.conf
At this stage we have decrypted group password in acme-vpnc.conf.
[Note: there is a site that can decrypt Cisco group password for you. Personally, I prefer relying on my own tools, that’s why I compiled my own decryption tool.]
Step 3) Setup vpnc configuration file (/etc/vpnc/ACME-vpn.conf)
Use your favorite editor to create your vpnc configuration file…
$ sudo nano /etc/vpnc/ACME-vpn.conf
Then add the following lines:
IPSec gateway nnn.nnn.nnn.nnn IPSec ID ACMEID IPSec secret fkvmdn34&3ldcmvnsbj#4%gB Xauth username alesk@pda-acme
Where:
- nnn.nnn.nnn.nnn — is IP address of VPN gateway (!Host variable in pcf file). It’s recommended that you use IP instead of fully qualified domain name for the gateway, to avoid problem of resolving DNS to IP!
- IPSec ID — is group name (!GroupName variable in pcf file)
- IPSec secret — is group password, originally encrypted in pcf file as !enc_GroupPwd variable. You must enter decrypted version of the password that you’ll find in vpnc configuration file generated in step 2.5
- Xauth username — username for authentication (Username variable in pcf file)
Step 3) Modify firewall rules to allow VPN connection
Use your favorite editor to edit firestarter user-pre file to add some iptables rules:
$ sudo nano /etc/firestarter/user-pre
Add the following lines (replace nnn.nnn.nnn.nnn with the Cisco VPN gateway IP):
iptables -A INPUT -j ACCEPT -s nnn.nnn.nnn.nnn -p esp iptables -A INPUT -j ACCEPT -s nnn.nnn.nnn.nnn -p udp -m multiport –sports isakmp,10000 iptables -A INPUT -j ACCEPT -i tun+ iptables -A OUTPUT -j ACCEPT -d nnn.nnn.nnn.nnn -p esp iptables -A OUTPUT -j ACCEPT -d nnn.nnn.nnn.nnn -p udp -m multiport –dports isakmp,10000 iptables -A OUTPUT -j ACCEPT -o tun+
Restart your firewall:
alesk@dbaportal:~$ sudo service firestarter restart * Stopping the Firestarter firewall... [ OK ] * Starting the Firestarter firewall... [ OK ]
Step 4) Test vpnc connection
You can start VPN connection either on the command line or with a GUI (Networker). To start VPN on a command line open Terminal and run:
$ sudo vpnc --natt-mode cisco-udp ACME-vpn
You’ll be first asked to provide password for the sudo, then you’ll be asked for the VPN password. After that you should see the standard welcome banner from your VPN provider. From this point onwards you have working VPN connection, you can open Terminal Service client and connect to your Windows workstation at work or whatever you want to do.
When you wish to close VPN connection simply run the following command in terminal window:
$ sudo vpnc-disconnect
Configuring VPN connection with GUI using Network Manager:
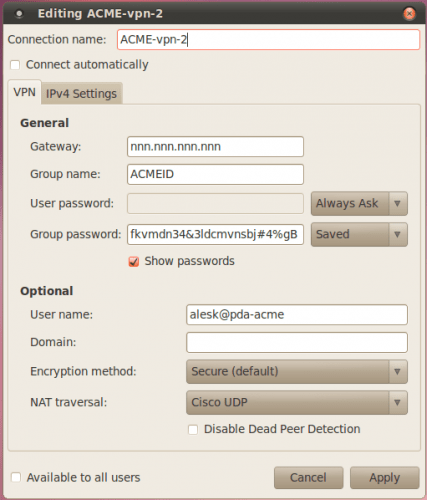
If you prefer to work with a GUI network manager you can setup vpnc connection with plugin that was installed in step 1. Here are some screenshots (let’s say I want to configure ACME-vpn-2 connection):
1) Open network manager (up and down arrow at the left)

2) Select “VPN connections”, then “Configure VPN”

* Don’t be confused by existing ACME-vpn, this is vpn that I already created.
3) Click on Add button to setup new VPN connection

4) From combo box select “Cisco Compatible VPN (vpnc)”

5) Fill the VPN tab with VPN data according to your setup
6) Also select IP4 tab and select “Automatic (VPN) addresses only

* Optionally enter (internal – inside VPN) DNS addresses.
Now, you can connect/disconnect from VPN by simply selecting VPN connection from Network Manager GUI.
Posted on 12.12.2010, in Linux, PostgreSQL, etc. and tagged Linux. Bookmark the permalink. Comments Off on How to install and use vpnc to connect to Cisco VPN concentrator.
You must be logged in to post a comment.